Okay, not the passwords themselves (those were in a Google Sheet, naturally). But we did Slack each other 2FA codes. Which is basically the same thing.
And it wasn't some scrappy five-person operation. This was a company with over $1B in funding, with smart people, real infrastructure, and no shortage of resources. The way we managed access to our brand's social media accounts was: someone had the password, someone had the phone, and everyone else had to ask nicely.
The Login Circus
I was on the marketing team at a well-funded, high-growth startup that had reached a $6 billion valuation. At some point, it became my job to update our social media bios — simple stuff, just keeping the copy fresh across Instagram, TikTok, X, YouTube. At most, an hour’s worth of work, theoretically.
In practice, it meant getting the password from our shared spreadsheet. Then logging in and immediately hitting an MFA wall. Then Slacking our social media guy to get the 2FA code, which had been sent to his phone. Then staying logged in on that exact device, on that exact browser, forever. Because if I ever logged out or tried from a different device, the whole comedy would start again.
This was a $6 billion company. With a small marketing team, sure, but still. The idea that access to our brand's social accounts was being managed through a chain of Slack messages felt insane even at the time. I can only imagine what this looks like at a company with fifty people in marketing, six agencies, contractors in three time zones, and twenty brand accounts across eight platforms.
Why Running Meta Ads Required a Zoom Call and a Driver's License
The social bio thing was annoying. This next one was genuinely alarming.
I needed access to our Meta Business account so I could start running paid ads. Seems simple, right? It wasn't.

Nobody on the current team could grant me access. You need an existing admin to approve it, and it turned out the only person with admin rights was one of our co-founders. Fine. I sent him a request. Except he hadn't logged in to Meta in a long time, so Facebook didn't recognize him and made him verify his identity. Which meant I had to get on a Zoom call with him, walk him through the process, watch him photograph his driver's license, and wait for Facebook to confirm it was really him.
Eventually, it worked. I got my access. I ran my ads.
One week later, that co-founder left the company.
I caught myself thinking: what if I had asked a week later? Would anyone have access to that account? Would the company have been locked out of its own Meta Business Manager and, by extension, its entire paid social operation? Would the answer have been “well, we’ll just have to wait and try to recover the account through Facebook support,” which, if you've ever done that, you know is its own special circle of hell?
The answer, almost certainly, is yes.
And this wasn't a one-off. This is how most social media accounts get managed: one person owns the login, a few others share access out of convenience, and when that person leaves — whether they're an employee, a contractor, or an agency contact — everyone else finds out the hard way. The account doesn't transfer. It just becomes inaccessible. Or worse, it stays accessible to someone who's no longer supposed to have it.
The Website That Went Down
Here's the part I still feel bad about, even though I tried to do everything right.
When I left, I was conscientious about offboarding. I made a list. I made sure other people had access to the accounts I owned: Braze, AppsFlyer, the marketing tools I lived in every day. I sent emails. I documented things. I was, by any reasonable standard, a good leaver.
I forgot about Vercel.
Vercel is the platform that hosted the company's website. My manager had given me admin access at some point, but during my time there, she ended up leaving the company. I became the only admin left on the account.
A few months after I left, I started getting frantic messages. The Vercel contract had lapsed. The renewal notice had gone to the account. Nobody could access the account to pay it. The website went down.
A $6 billion company's production website. Down. Because one ex-employee forgot he was an admin on a platform, and nobody had a system to catch it.
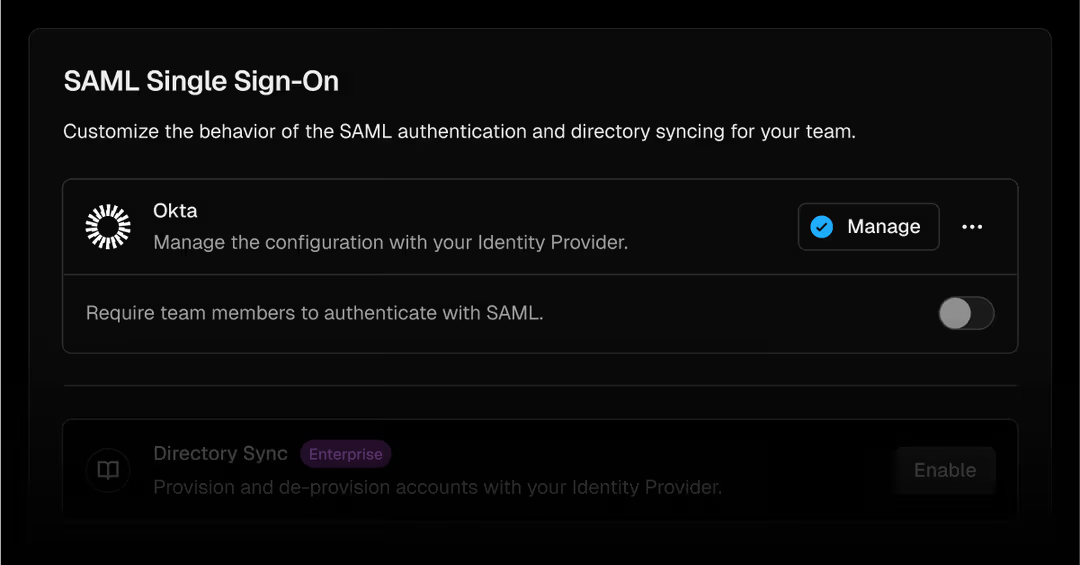
The kicker? Vercel does offer enterprise-grade identity controls, including SAML SSO and SCIM, which together would have meant the account was tied to the company's identity system, and my access would have been removed automatically when I left. But at the time, those features were only available on their enterprise plan, which we weren't on. We were caught in the gap that exists across most organizations: the controls that would actually solve the problem are real, they exist, but they sit behind a pricing tier most teams never reach. So the app stays disconnected, the risk stays live, and someone like me ends up being the single point of failure without anyone realizing it, including me.
This Isn’t One Company’s Problem
I'm not telling these stories to embarrass anyone. The people I worked with were smart and hardworking. This happened because it happens everywhere.
According to new research from the Ponemon Institute, commissioned by Cerby and based on a survey of 614 IT and security leaders, 68% of organizations report delayed or incomplete access removal after an employee leaves. Not a few rogue startups. Not just small teams. Nearly seven in ten.

The same research found that 77% of organizations experienced at least one cybersecurity incident in the past two years caused by their inability to secure disconnected apps, the apps that sit outside the centralized identity stack. Social media platforms. Marketing tools. Ad platforms. The stuff that marketing teams run every day with zero IT oversight and whatever credentials someone set up two years ago.
And here's the stat that really lands: 34% of incidents involving disconnected apps specifically included social media platforms like Meta, LinkedIn, X, and Instagram. The exact apps my team was managing through shared passwords and Slack-message MFA codes.
The Part IT Doesn’t Always See
What makes this hard to solve is that the people feeling the pain are marketers, not IT. Marketers don't file tickets that say “I had to text Joe three times to get the MFA code again.” They just deal with it and move on.
Meanwhile, IT is looking at identity coverage metrics that reflect the connected apps — the ones with SSO — the ones that play nicely with Okta or Entra ID. Those numbers can look pretty solid. What they don't show is the parallel universe of marketing tools, social platforms, and ad accounts that were never integrated, either because they don't support identity standards, or because, like Vercel, SSO was locked behind a pricing tier the company wasn't on.
The Ponemon research puts a number on this. On average, organizations have 80+ applications sitting outside their identity control plane, roughly 32 of which are business-critical. Social accounts and marketing tools make up a meaningful chunk of that, and they’re being managed with whatever combination of shared spreadsheets, password texts, and Slack messages the marketing team has cobbled together.
What “Good” Actually Looks Like
The Meta situation could have been a disaster. It wasn't, but only because I asked the right person at exactly the right time. That's not a system. That's luck.
The Vercel situation wasn't luck. That one actually broke something, and it happened even though I genuinely tried to do the right thing on my way out.
A real system ties every account to corporate identity rather than to individual employees. Access is granted and revoked automatically when someone joins or leaves. MFA works without one person being the keeper of the codes. When an admin leaves, their access is automatically cleaned up across every app, not just the ones IT already manages.
That's what Cerby does, specifically for the apps that identity tools can't reach natively: the ones without SCIM, the ones where SSO is a premium add-on nobody bought, the ones that live in the marketing stack with a dozen people who “sort of have access” and nobody actually in charge.
The Bigger Picture
The Ponemon research found that 63% of organizations have failed an audit at least once because of gaps in securing disconnected apps. And only 34% of organizations say they can consistently produce complete and accurate access records for those applications.
Think about what that means in practice. An auditor asks: who had access to your social media accounts over the past 12 months? When was it granted, when was it revoked, can you show me the log? Most marketing teams would reconstruct that from memory and email threads. That's not audit-ready. That's audit-exposed.
And it’s getting worse. 58% of organizations say the number of disconnected apps increased over the past 12 months, driven largely by AI tools that employees adopt without IT involvement, most of which don't support enterprise identity standards.
What To Do With This
If you're in marketing and any of this sounds familiar, you're not alone. This is the default state for most marketing teams, and it's not because anyone is careless. It's because the tools weren't designed for enterprise access management, and nobody gave you a better option.
If you're in IT or security, the marketing stack is probably one of the least-visible corners of your identity program. But it shows up in breach reports, audit findings, and incident logs.
The Ponemon research we commissioned goes deep on exactly this problem: the security, compliance, and operational cost of disconnected apps, based on 614 IT and security leaders across industries. If you're trying to make the case internally that this deserves attention, it's worth a read.


