Today, we are announcing a milestone in our journey: a $12 million seed funding round from Ridge Ventures, Bowery Capital, Okta Ventures, Salesforce Ventures, and others, bringing total funding to $15.5 million.
Approaches for dealing with shadow IT are broken. Despite it being a $400B problem and a major pain for every business, existing methods do not work. After personally spending years in the tech industry, first at Google and then as co-founder at Ooyala, my co-founders and I saw this problem repeatedly. The founding team, including myself and Vidal González, decided it was time to fix this problem and build a company that flips the script – a shadow IT solution that delivers visibility, control, automation, and a beautifully designed interface that non-technical users can easily understand. I know…cybersecurity and beautifully designed interfaces don’t typically go hand in hand, but we are changing that.
Shadow IT has historically been defined as non-IT employees' unauthorized use of applications. The applications are provisioned, managed, and used by non-IT employees and typically unlock a Pandora’s box of security vulnerabilities. While the term shadow IT broadly encompasses many applications, it glosses over the fact that the majority of these applications do not support common security standards. Namely, SAML for authentication (think single sign-on) and SCIM for adding and removing users. Without support for these standards, we think there is a better name for this group: unmanageable applications.
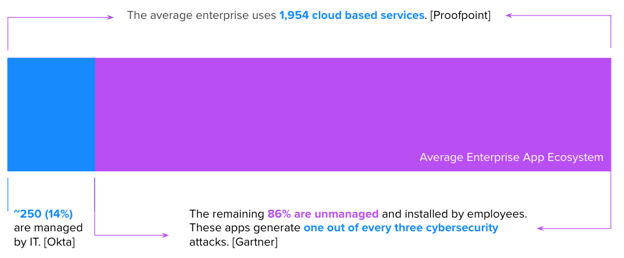
To put it bluntly, unmanageable applications are those that do not support industry standards like SAML and SCIM and are typically selected and on-boarded by individual business units outside the purview and visibility of IT and Security. These applications in the enterprise are exactly what we call them: unmanageable in their current state. According to Gartner, these applications are responsible for one of every three cybersecurity attacks.
Unmanageable applications are creating a massive attack surface
Our investors
Today, we are announcing a milestone in this journey: a $12M seed funding round led by Ridge Ventures, Bowery Capital, Okta Ventures, Salesforce Ventures, and others. In a matter of 15 months, we’ve gone from concept to landing some of the world’s most recognizable brands including L’Oréal, Dentsu, Televisa, and Wizeline. This investment is proof of our progress and the amazing market opportunity we have to change how unmanageable applications are addressed in the enterprise. We are excited to have the brainpower of Yousuf Khan, Partner at Ridge Ventures, and former CIO, as well as Michael Brown, Founder, and General Partner at Bowery Capital, join our board.
Taking on an industry problem
Companies building SaaS applications struggle to ensure a robust security architecture around the identity layer (a key tenant of zero trust). While many do integrate into an identity access management solution (IAM) like Okta or Azure AD, most SaaS applications only support individual account use. Social media apps, for example, which have largely been used by consumers and now are central to being used by corporate marketing and PR teams, aren’t fit for enterprise identity management. Other examples that fall into this category include financial services and healthcare platforms that are often mandated by regulators.
Our research indicates that businesses attempt to close this gap with a combination of identity providers (IDPs) like Okta, enterprise password managers (EPMs), and other network-based solutions like cloud access security brokers (CASBs) and security service edges (SSEs). The problem with this approach is that while IDPs have pioneered a full application lifecycle management approach, it only works for applications that support standards (e.g., SAML and SCIM). EPMs only manage the password (a tiny part of the overall identity and access management lifecycle) and CASBs and SSEs typically block access to unmanageable applications entirely. This combination of solutions doesn’t work, as we found out in our most recent analysis.
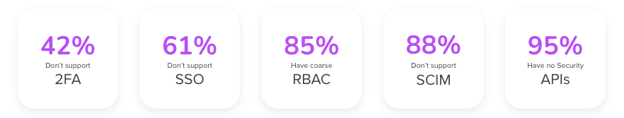
The facts on unmanageable applications
Source: Cerby research
We worked with Osterman Research to engage over 500 business professionals across the US and UK. The findings indicate that employers should strongly consider investigating solutions that accommodate this new normal of employee application choice, post-COVID. The most interesting stat? 92% of employees and managers want full control over the applications they use for work.
Given this finding, enterprise executives, particularly CIOs, CMOs, and CISOs are desperate for a solution; and this is precisely why we created Cerby. No other platform significantly lowers unmanageable application risk by incentivizing non-IT users to register their applications while automating the entire application lifecycle.
Curious how Cerby does its magic?
You can watch a demo here but Cerby works using a combination of robotic process automation and application APIs, enabling Cerby to create points of structured control even when the SaaS application itself does not expose them.
Cerby leverages a number of automation agents (e.g., a browser plugin, a local desktop client, and a server-side isolated browser) to play back programmed automation flows. This allows the Cerby platform to securely manage and automate key security hygiene tasks for any application without being limited by the platform’s underlying APIs (a major limitation of CASBs and SaaS Security Posture Management platforms). This is a key sticking point for many existing cybersecurity solutions–they are limited by the application's APIs. Cerby doesn’t have this problem.
Our team
In 2007, I co-founded my first startup. Then, 2008 happened. The Great Recession forced us to focus and question our decisions and investments rigorously. I learned that great companies can be built in downturns but most importantly, I learned that small, good habits when accrued over time lead to big outcomes. Today, this is one of our core values. As Cerbenauts (what we call ourselves), we make the bed every morning knowing that in periods of uncertainty, focusing on small wins every day leads to success.
With decades of combined experience in the technology industry and several successful startups under our belts, we know what it takes to build a company for the long haul. We have deep knowledge both in the cybersecurity industry as well as complimentary fields such as consumer video (which is why we know how to build a beautiful user experience!). Our knowledge combined with our unique experience across multiple startups sets Cerby up to lead a new generation of unmanageable application solutions and become a trusted partner in the industry.

What lies ahead
With the seed investment helping to fuel our growth through the remainder of 2022, we plan to scale our product, our customer base, and our team (we are hiring and we won’t rescind offers!). Here’s to a new approach to taming the unmanageable. Will you join us?

