© 2025 Cerby All Rights Reserved
Cerby vs SaaS Management | Cerby vs PAM | Cerby vs EPM | Cerby vs IGA | Cerby vs IDP | Trust & Transparency | Privacy Policy | Accessibility | Terms of Service
New Ponemon Report: The Hidden Cybersecurity Threat of Disconnected Apps | Download Now →





The Ponemon Institute found that 52% of organizations have experienced a cybersecurity incident due to the inability to secure nonstandard applications. The average cost of manually onboarding and offboarding users from nonstandard applications is $1,000 per employee.
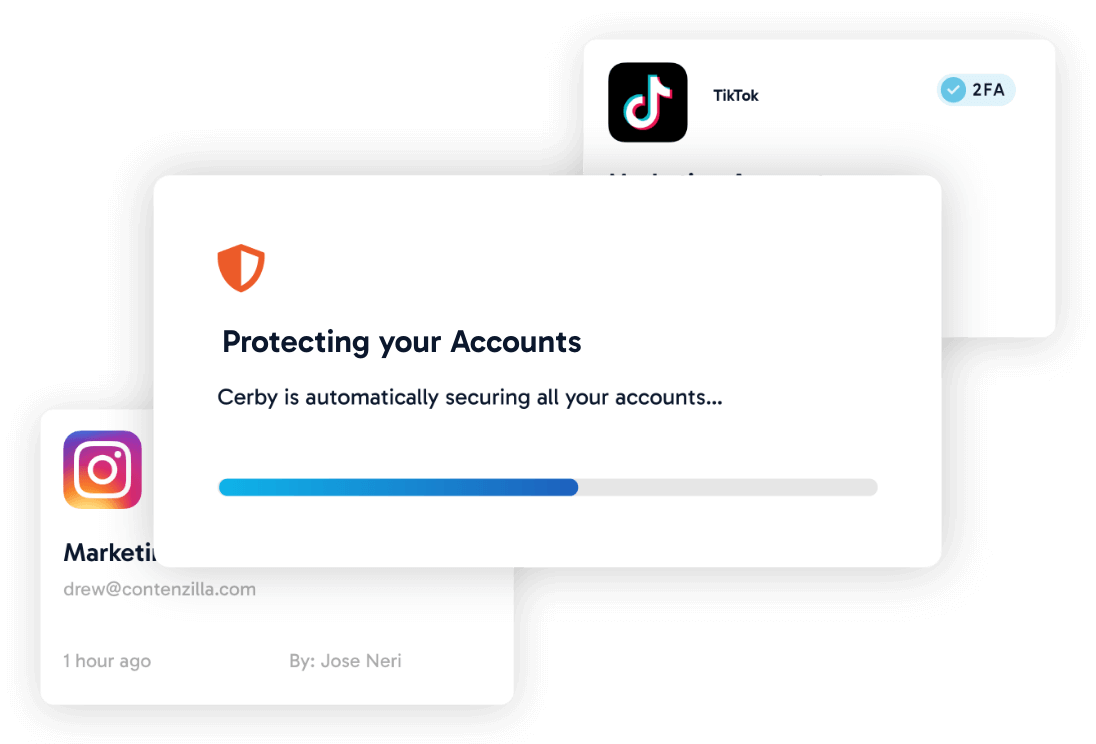
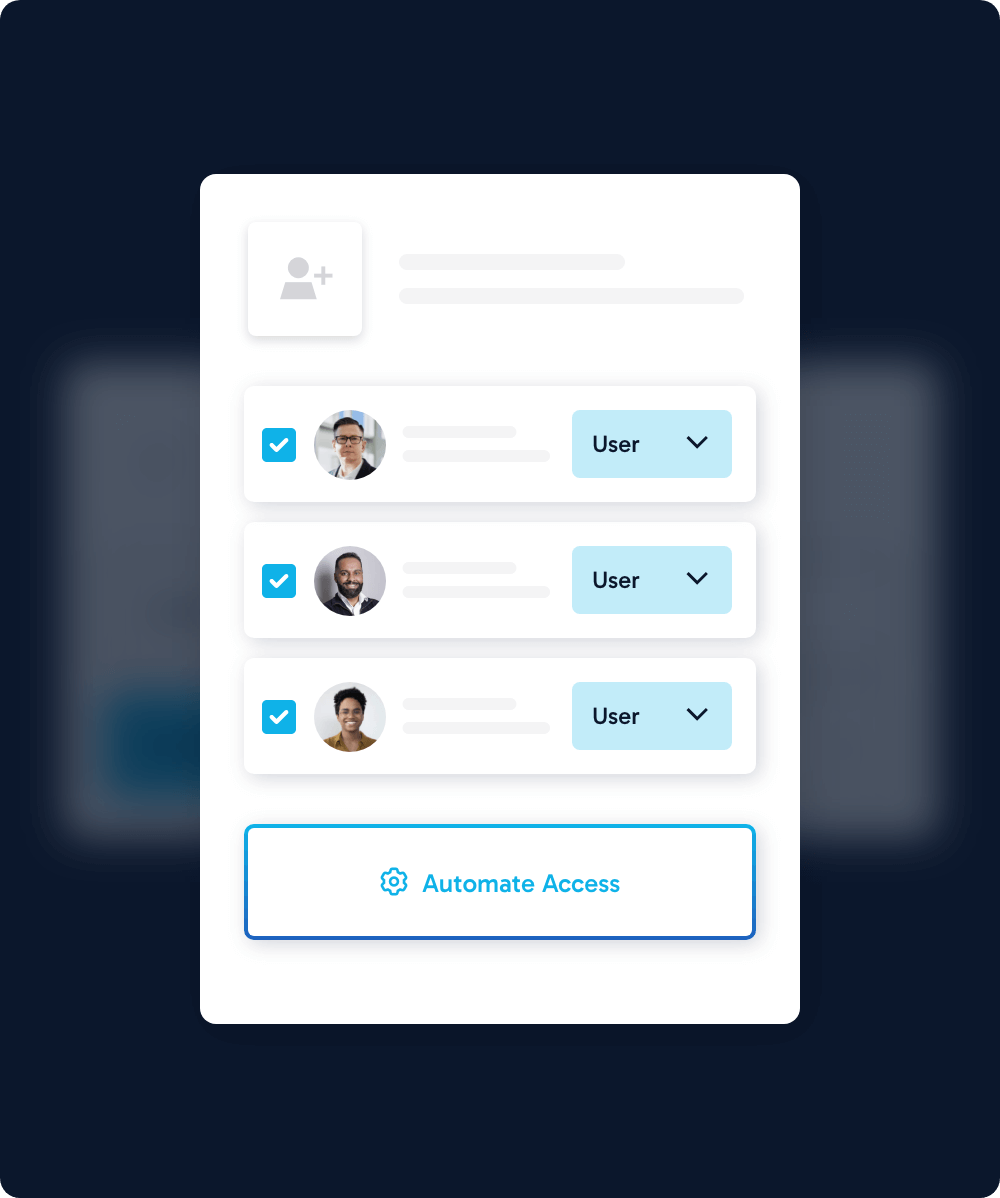
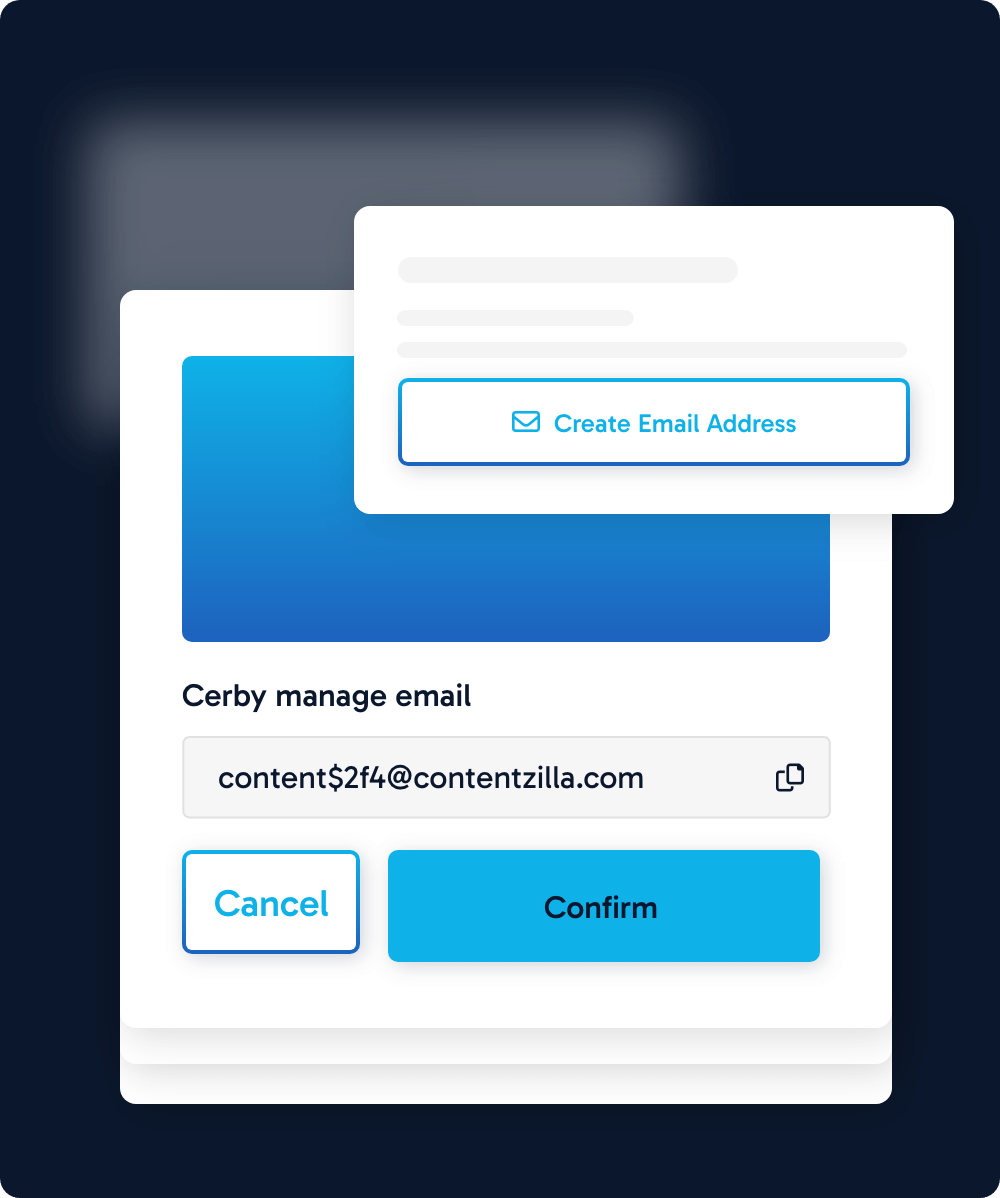
Cerby mitigates the cyber risk and financial impact by bringing any nonstandard application into the identity lifecycle of your existing workforce identity platform, e.g., Okta, Azure AD (Entra ID), Ping, etc., removing the need for enterprise password managers and lifting the compliance burden of managing these apps manually.
Our patent-pending platform has two pillars: our access orchestration engine and extensive application catalog. Cerby maps each supported application and extends your IDP with protocols, robotic process automation, and application APIs to create points of programmatic control even when the app itself does not expose them.








Cerby natively supports many applications right out of the box, and we add more regularly. Don’t see your application listed below? Don’t worry, we've got you! Request an integration below. And yes, we natively integrate with Okta, Azure AD (Entra ID), Ping, and any standards supporting IDP.











